 The idea of physical security is changing rapidly at a time when our physical health and safety require us to rethink the very nature of our relationship with the physical world.
The idea of physical security is changing rapidly at a time when our physical health and safety require us to rethink the very nature of our relationship with the physical world.
Yes, there are still facilities, hotels, airports, office buildings and other physical locations. For the most part, these venues continue to be active, with employees, visitors and vendors on the premises. And in all of these places, the threat still exists for unauthorized intrusion, theft, workplace violence and other risks. As ever, key control is still one of the best ways to minimize those threats and protect organizations by mitigating vulnerabilities.
Yet during a global pandemic, there are new considerations that need to be taken into account. Even with excellent sanitation procedures, many users will not want to touch a keypad to input a PIN number every time they need to retrieve or return their keys.
Learn more about best practices for sanitizing your KeyWatchers
Facial recognition can solve this challenge for key control users, greatly reducing shared touchpoints and helping to curb the spread of viruses and bacteria. At the same time, this technology delivers multiple additional benefits.
While it is not uncommon for access control users to lose their ID or prox cards, or to forget to carry them, your face is always with you. You will never have to search your pockets or scrabble through a backpack or purse to find it. You might forget your PIN code, but you cannot forget your face.
Additionally, if an organization is already using the technology in other areas of the facility, it is easy to integrate facial recognition with key control cabinets. By doing so, you can simplify access control across the organization, saving costs and streamlining operations.
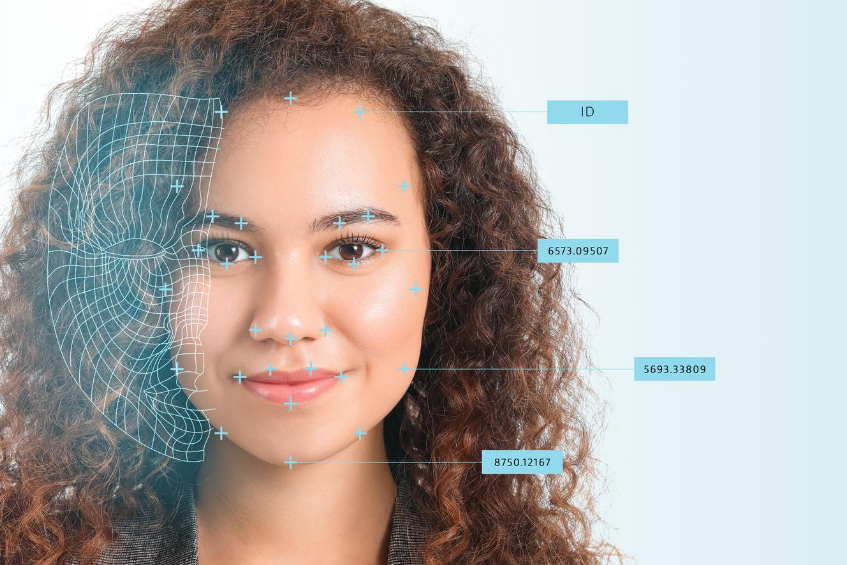
The user experience is simple and convenient. With key control integrated with facial recognition, the user simply presents their face to the reader to request access. The facial recognition software scans their face, reading a number of different geometric vectors such as the distance between eyes, or from chin to forehead, to look for a match with photos in the user database. Depending on the sophistication of the software, it may be reading 50, 75 or more different factors. Each analysis is performed in seconds. If the software finds a match with an identity in the database, the permissions for that identity are applied to the person seeking access and the appropriate keys are released.
When introducing new facial recognition technology to a workforce, it is helpful to be prepared for some of the more common questions. Often these are based on a limited knowledge of the technology, combined with some outdated myths. For example, it has been said that facial recognition is inaccurate, or that it will be used to track individuals beyond the basic access control it enables. As an administrator or provider, you can alleviate those concerns with factual information.
As a technology, facial recognition for security is more accurate than ever. In truth, the level of accuracy has improved enormously in the last 10 years, according to an evaluation performed by the National Institute of Standards and Technology’s (NIST). The failure rate for searches, meaning that the software failed to find the matching face residing within a database, has dropped from 5% in the year 2010 to just .2% in 2018 – a reduction of 96%.
And while the capability of tracking every individual is theoretically not beyond the power of the software, the cost and bandwidth it would take to do so vastly outweighs any benefits that might exist. The only data stored on facial recognition user databases is the physical information contained in the photos themselves, along with the identities of the individuals in the photos.
For access that delivers better physical safety for the user, along with fast and accurate security for the organization, facial recognition is an excellent choice. It’s truly a technology that is right for this moment.
Read more about how our recent product enhancement help fight the spread of microbes and bacteria to combat potential threats to personnel health.



